 In our last post, we talked about the fact that we got hacked because of TimThumb vulnerability. While fixing the vulnerability, I realized that, we were not the only one who got hacked. Plenty of websites using TimThumb to resize their images, got hacked. So, I thought of putting together a nice step by step guide on how to recover from this kind of hack. Please note that, while the nature of the hack may vary, we are trying to give an overall idea on recovering. I will focus mainly on WordPress themes using timthumb but, as I had other infected sites, I will discuss about disinfecting general php files too. This topic will cover
In our last post, we talked about the fact that we got hacked because of TimThumb vulnerability. While fixing the vulnerability, I realized that, we were not the only one who got hacked. Plenty of websites using TimThumb to resize their images, got hacked. So, I thought of putting together a nice step by step guide on how to recover from this kind of hack. Please note that, while the nature of the hack may vary, we are trying to give an overall idea on recovering. I will focus mainly on WordPress themes using timthumb but, as I had other infected sites, I will discuss about disinfecting general php files too. This topic will cover
- Get to know if your site is hacked
- How the hack has occured
- Cleaning your WordPress site
- Cleaning your general PHP files
- Searching the last trace of injected code using SSH
#1: Get to know if your site is hacked:
If you are an experienced webmaster then you probably know whether your site is hacked or not. If not, then there is a number of ways. The best way is to check using google webmaster.
- If your site is registered at Google Webmaster then you probably have got a message related to badware activity.
- If not then just visit StopBadware and check to see if there is any malware activity or not.
In most cases, it takes a while before Google detects malware on your site and gives you the warning. You can check even before that for any possible malwares. The common symptoms are
- Malicious codes like
<script type=”text/javascript”>eval…
on your HTML pages.
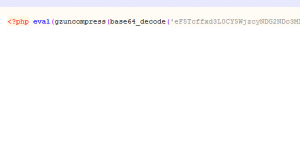
- Malicious codes like
<?php eval(gzuncompress(base64_decode(‘eF5Tcffxd3L0CY5WjzcyN..
on your PHP pages.
- Unknown advertisements being shown on your site.
and etc etc…
#2: How the hack has occured:
In previous version of timthumb there was a vulnerability. The following sites were whitelisted by the script for remote image loading and resizing.
‘flickr.com’,
‘picasa.com’,
‘blogger.com’,
‘wordpress.com’,
‘img.youtube.com’,
);
But, the author has used the PHP function strpos to verify whether the request has been made from whitelisted sites or not. Like in my case a request to the timthumb was made using the following URL:
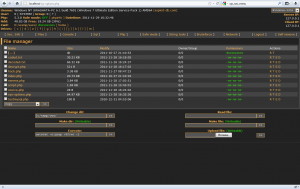
As you can see it asked timthumb to fetch an image from http://blogger.com.n*****u.com/config.php which is not actually an image file, the timthumb script copied that php file to the cache directory. Now as obvious, the PHP script can be executed directly from that cache directory and endlessly possible things can be done with it! In my case a shell was uploaded which looked like this.
NOTE: To take the above screenshot, I had decrypted the uploaded file and ran it on my localhost. Usually the files being uploaded are heavily encrypted and requires a password (md5 encoded) to gain access.
After that, the hacker used that shell to inject bad codes to all the index.php, footer.php, index.html files on my server.
#3: Cleaning your WordPress website:
In most of the cases the hack comes from a WordPress theme using timthumb to resize images. In order to clean your site, you first need to reinstall WP and then take preventive measures to stop this hack.
#3.1: Clean and reinstall WP:
At this point many of your WordPress files including all index.php and wp-config.php are injected with malicious code. A script resides in your cache directory which allows the hacker to gain access to your server and many copy of that script has been put in different directories. The best way is a cleaner installation of WordPress.
- Change the DataBase password of your WordPress DB using your WebHost. This is very important.
- Download all the files from wp-content directory. We shall use only the uploads directory to save your images.
- Manually check each sub directories under /wp-content/uploads directory and delete all the files with a .php extension. Any PHP file found here should be a copy of the script. In my case a few PHP scripts with names like sys-options.php, new-classes.php, meta-tags.php were found. Make sure you delete them. After cleaning all these mess, retain a copy of the upload directory.
- Delete everything under your Website’s public_html directory. Yes, everything. This ensures that no copies of the script is left.
- Download a fresh copy of WordPress. Edit the wp-config.php file and put in the database details and salt details manually. You should enter new salts from the WordPress Online generator.
- Upload the fresh copy of WP (with edited wp-config.php file) to your site’s public_html directory. Then navigate to http://yoursite/wp-admin … If required this will update the database of your WP setup. Then login to the Dashboard.
- At this point, you don’t have the image files. There is no need to panic though. Just upload the cleaned /uploads directory to wp-content and you are all done.
Now, it’s time to fix your theme.
#3.2: Cleaning the WP theme and update timthumb:
Many of the files of your theme should be hacked. Best is you download a fresh copy of your theme. If you have modified your theme, then you have to check in all php files manually and find and delete any trace of malicious code (You should probably know how to do, as you have modified your own theme 😉 ). Once done, update the timthumb with the latest code. It can be found here.
Now simply upload the theme and activate it from WP admin panel. You are all done.
#4: Cleaning general PHP & HTML files:
This can be quite hectic. In my case many static HTML and PHP files were injected with malicious codes. The only way is, check your files individually and remove them. You can also use editors like NetBeans to perform a search (search for ‘eval‘) over a collection of files to quickly find all the infected files.
Once found, clean them by deleting the codes and upload them to your server.
#5: Searching the last trace of hack using SSH:
This is very important. If you have access to SSH, then just type this command
grep -r base64_decode *
If you see any occurrence of this then you better investigate the file manually for any possible infection. If there is a long encoded string then probably that’s a bad code which you don’t want to keep.
So, that was all about how to fix this vulnerability and clean your site. Hope you have find it interesting and informative. Do not forget to add in your thoughts!
You should also mention that users that dont know is their site is vulnerable to this “exploit” can check it by installing this plugin http://wordpress.org/extend/plugins/timthumb-vulnerability-scanner/.
I’m glad you’re back in business 🙂
I am glad too 🙂 .. And thanks for the plugin information. It should really help those who are not that good in coding!
I am often to blogging and i really appreciate your content. The article has really peaks my interest. I am going to bookmark your site and keep checking for new information.